In this article we will shed some light on the Underground Software Tools Hackers Use; basically what are the powerful and legal Cyber Security tools ethical hackers use to find vulnerabilities, check system security and protect digital environments with these tools.
They are also used extensively by professionals in penetration testing tools, networking analysis and malware research to protect the web (with permission).
Key Point & Underground Software Tools Hackers Use (Legal & Safe)
| Tool | Legal Use Case |
|---|---|
| Burp Suite | Web app penetration testing |
| Nmap | Network auditing & monitoring |
| Wireshark | Troubleshooting & security analysis |
| Metasploit Framework | Ethical hacking & vulnerability validation |
| John the Ripper | Password strength auditing |
| Hydra | Authorized authentication testing |
| Nikto | Website security assessment |
| SQLmap | Secure database validation |
| Maltego | OSINT & threat investigation |
| Cuckoo Sandbox | Cyber threat research |
1. Burp Suite
One of the most critical tools used by ethical hackers in a black box testing phase is Burp Suite, an incredibly powerful platform for testing web application security. It functions as an intercepting proxy, capturing requests and responses from the browser to facilitate professionals in identifying vulnerabilities including but not limited to XSS, authentication issues, and insecure sessions.
Burp Suite is one of the most mentioned Underground software tools hackers use because it can be automated when you want a web scan, but gives manual testing as well. These features include Intruder, Repeater, and Scanner which are utilized by security researchers to safely simulate real-world attacks.
Burp Suite is also used legitimately by developers and penetration testers to fortify web applications, enhance coding practices, check sensitive user data security from cybersecurity attacks.
Burp Suite — Major Features
- Real time interception and modification of HTTP/HTTPS requests.
- Web application automated vulnerability scanner.
- Intruder tool for checking authentication and input validation.
- Manual request analysis through the Repeater function
- Advanced reporting system for results of security assessment.
Burp Suite
| Pros | Cons |
|---|---|
| Powerful web vulnerability scanner | Professional version is expensive |
| Excellent manual testing tools | Steep learning curve for beginners |
| Real-time request interception | Can slow browser traffic |
| Detailed reporting features | Requires technical knowledge |
| Industry-standard penetration testing tool | Advanced setup needed |
2. Nmap
Nmap stands for Network Mapper, open-source tool that is widely respected and used in discovering network devices. This helps the ethical hacker to determine open ports, services being run, operating systems and the vulnerabilities in that network. Named as Underground Software Tools Hackers Use, Nmap gives a peek into infrastructure security at no cost of damage.
It is used by system administrators to audit networks, monitor exposure points and identify unauthorized devices. It has an extremely flexible scripting engine that enables automated vulnerability checking. Nmap, when employed in a legal manner, aids organizations by enabling them to grasp their attack surface prior to malicious actors attempting exploitation, which enhances cybersecurity posture.
Nmap — Key Features
- Network discovery and host identification.
- Finding open services by port scanning
- Operating system detection capability.
- Automation with Nmap Scripting Engine (NSE)
- Network mapping and vulnerability detection.
Nmap
| Pros | Cons |
|---|---|
| Fast network discovery | Command-line usage may confuse beginners |
| Highly customizable scans | Incorrect scans may trigger alerts |
| Open-source and free | Requires networking knowledge |
| Accurate port scanning | Limited GUI features |
| Powerful scripting engine | Results need expert interpretation |
3. Wireshark
Wireshark Overview Wireshark is a network packet analyzer. Cybersecurity analysts use it to diagnose performance issues, detect suspicious activity, and study communication protocols. Wireshark — Wireshark is a free and open-source packet analyzer; it enables users to capture and interact with the traffic being transmitted over their networks as one of Underground software tools that hackers use.
Ethical hackers utilize it when they are performing penetration testing in order to discover insecure transmissions or data leaks. With its graphical interface and powerful filtering options, analyzing complex traffic becomes simple, allowing organizations to ensure secure communication channels and prevent unauthorized access.
Wireshark — Key Features
- Network Packet Capture And Inspect In Real Time
- Protocol level deep analysis across thousands of protocols.
- Advanced display filters for traffic analysis.
- Detailed packet-level troubleshooting tools.
- They support live capture and offline analysis.
Wireshark
| Pros | Cons |
|---|---|
| Deep packet inspection capability | Complex interface |
| Supports hundreds of protocols | High learning curve |
| Excellent troubleshooting tool | Large captures consume memory |
| Free and open-source | Not designed for active attacks |
| Advanced filtering system | Requires networking expertise |
4. Metasploit Framework
The Metasploit Framework is an industry-leading platform for penetration testing that allows an organization to conduct simulated attacks in a controlled environment. It’s used by security professionals to see which known vulnerabilities can work within systems.
Metasploit — Known as one of Underground Software Tools Hackers Use, Metasploit is full of exploit modules, payloads, and auxiliary tools. Ethical hackers and pen testers perform safe simulations to identify vulnerabilities, address weaknesses, and review security controls.
The framework is designed to allow for post-exploitation testing, helping analysts gain insight into how attackers may act in any specific environment. Organizations gain practical insight by legally emulating attack scenarios, empowering them to assess their security posture, and enhancing incident response strategies before the real threats arrive.
Metasploit Framework Key Features
- Extensive database of exploits and payload modules.
- Automated penetration testing workflows.
- Post-exploitation and privilege escalation testing.
- Integration with vulnerability scanners.
- Custom exploit development support.
Metasploit Framework
| Pros | Cons |
|---|---|
| Huge exploit database | Requires advanced skills |
| Automates penetration testing | Can be misused if unauthorized |
| Strong community support | Resource intensive |
| Post-exploitation testing tools | Setup complexity |
| Widely trusted by professionals | Not beginner-friendly |
5. John the Ripper
John the Ripper is a password cracking software used to perform dictionary attacks on passwords. This tool tests large wordlists and cracking techniques against encrypted password hashes to reveal weak credentials. As part of Underground Software Tools Hackers Use, the tool helps organizations identify weak password policies before they are leveraged by attackers.
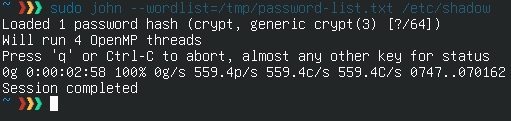
Audits are controlled by ethical hackers and system administrators to guarantee that accounts are secured with strong authentication practices. Supporting various hash formats and operating systems, John the Ripper also provides a detailed analysis of credential vulnerabilities to help organizations implement stronger password policies and minimize unauthorized system access.
John the Ripper Key features
- Fast password hash cracking engine.
- Supports multiple encryption formats.
- Dictionary and brute-force attack modes.
- Password strength auditing capabilities.
- Cross-platform compatibility.
John the Ripper
| Pros | Cons |
|---|---|
| Fast password auditing | Command-line focused |
| Supports many hash formats | Requires strong hardware for speed |
| Helps enforce password security | Limited graphical interface |
| Open-source availability | Needs technical understanding |
| Flexible cracking modes | Time-consuming for strong passwords |
6. Hydra
Hydra is a very fast and flexible login assessment security tool which support many different services. Hydra To Perform Brute-force Attack (Among Underground Software Tools Hackers Use) It is used not for illegal hacking, but exploring weak login mechanisms and poor credential protection.
Security testers invoke attack speed, set up wordlists, and a wide range of services in order to see how things respond with pressure applied. Results from Hydra help the organizations to apply policies of account lockouts, multi-factor authentication and stronger password policies so that credential-guessing attacks through automated methods cannot be carried out on systems.
Hydra — Key Features
- High-speed login credential testing.
- Basically it accepts SSH, FTP, HTTP, RDP protocols.
- Run mutiple attacks in parallel for fast results.
- Custom wordlist configuration.
- Authentication security testing automation.
Hydra
| Pros | Cons |
|---|---|
| Extremely fast login testing | Can lock accounts during testing |
| Supports many protocols | Requires authorization |
| Lightweight and efficient | Command-line based |
| Customizable wordlists | Not beginner friendly |
| Useful for authentication audits | Detection by security systems |
7. Nikto
Nikto is a free & open-source web server scanner that detects outdated software, dangerous files, and server misconfigurations. It is one of the Underground Software Tools Hackers Use according to ethical hackers since it can quickly scan thousands of known vulnerabilities on various websites. Nikto looks for SSL problems, insecure scripts, default installations and exposed directories that attackers tend to target.
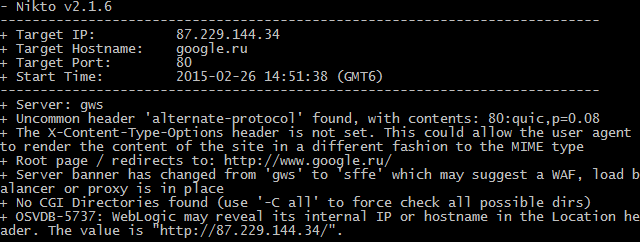
The results help security professionals to enhance server hardening methods and upgrade susceptible components. Nikto is easy to run but delivers detailed reporting, which assists admins in prioritizing fixes and ensures web infrastructure’s security continues as cyber threats evolve.
Nikto — Key Features
- Performs scans of servers to identify outdate software versions.
- Detects dangerous files and scripts.
- Identifies server misconfigurations.
- SSL and security header testing.
- Detailed vulnerability reporting.
Nikto
| Pros | Cons |
|---|---|
| Easy vulnerability scanning | Generates many false positives |
| Detects outdated software | Limited modern GUI |
| Open-source tool | Basic reporting design |
| Quick server assessment | No advanced exploitation features |
| Simple command execution | Requires manual verification |
8. SQLmap
SQLmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over database servers. Databases contain sensitive business and user data, making them a prime target for attackers.

SQLmap helps ethical hackers to find sas database queries vulnerable to criminals before they become a very big target of criminals one among the Underground Software Tools Hackers Use.
It automates this process for payload testing, database fingerprinting, and vulnerability verification while working under the right conditions. SQL offers web app security teams a method to identify issues through input/output validation and lock down how user data is processed in the web application.
SQLmap — Key Features
- Automated SQL injection detection.
- Database fingerprinting and enumeration.
- Supports multiple database management systems.
- Data extraction testing under authorization.
- Command-line automation for penetration testers.
SQLmap
| Pros | Cons |
|---|---|
| Automates SQL injection testing | Command-line complexity |
| Supports multiple databases | Requires authorized testing |
| Powerful database enumeration | Can be slow on large targets |
| Highly accurate detection | Advanced usage learning curve |
| Saves time during audits | May trigger security alerts |
9. Maltego
Maltego is a link analysis and open-source intelligence (OSINT) tool used for forensic and investigative tasks. It is used by cybersecurity researchers to create a map of relationships between domains, emails, IPs, organizations and individuals.
Part of the Underground Software Tools Hackers Use, Maltego converts scattered public information into visual graphs that expose hidden links. Ethical hackers use it during the scanning phase to gain a legal understanding of potential attack surfaces.
In addition, investigators, journalists and threat analysts also use Maltego for fraud detection and cybercrime research. With its ability to visualize, it accelerates intelligence analysis for cybersecurity operations into the actionable stage and simplifies understanding.
Maltego — Key Features
- Graphical relationship mapping and labeling.
- Open-source intelligence (OSINT) gathering.
- Open data — Entity discovery from the Public Data.
- Custom transform integrations.
- Graph-based investigation interface.
Maltego
| Pros | Cons |
|---|---|
| Visual intelligence mapping | Free version has limits |
| Excellent OSINT capabilities | Requires internet data sources |
| Easy relationship analysis | Premium features costly |
| Useful for investigations | Needs analytical skills |
| Professional investigation tool | Data accuracy depends on sources |
10. Cuckoo Sandbox
Cuckoo Sandbox allows for automated malware analysis by safely executing suspicious files in isolated virtual environments. Security researchers study how unknown applications act without endangering real systems.
Underground Software Tools Hackers Are Using Cuckoo Sandbox : helps researchers watch file activity like registry changes, network connections, and bad behavior. Ethical hackers and incident response teams use it to study ransomware, trojans, and spyware samples on a legal basis.
The sandbox generates detailed behavioral reports that the organizations can use to build better defenses, update antivirus signatures, and respond quickly when new cyber threats trigger alarm bells.
Cuckoo Sandbox — Features
- Execution of malware is a sandbox environment.
- Automated behavioral analysis reports.
- Network traffic monitoring during execution.
- File and registry activity tracking.
- Threat intelligence integration for research.
Cuckoo Sandbox
| Pros | Cons |
|---|---|
| Safe malware execution | Complex installation |
| Automated behavior reports | Requires virtualization setup |
| Detailed threat analysis | High system resource usage |
| Open-source flexibility | Maintenance required |
| Valuable for research teams | Advanced configuration needed |
Conclusion
Cybersecurity is a world of wolves — but many Underground Software Tools Hackers Use are totally legal and necessary for helping protect digital systems! For instance, ethical hacking is more about defense than offense employing tools like Burp Suite, Nmap, Wireshark, and Metasploit Framework. Cybersecurity experts leverage these platforms to detect vulnerabilities in their systems and fortify infrastructure, so real-life cyberattacks can be avoided preemptively.
What makes these tools “underground” is in fact not an illegality, but their powerful capabilities frequently misconstrued by newcomers. Responsible use transforms them into a learning environment for penetration testers, developers, network admins, and security researchers. In our interconnected and tech-oriented world, ethical hackers are essential for organizations to recreate attacks, assess systems, and uphold user information security.
Ultimately, cybersecurity is about education and accountability. By understanding how attackers think, a defender can build better protections. This could result in a person or organization being aware of and using these high-level security tools properly, going from being potential victims to becoming active fighters against emerging threats.
FAQ
What are Underground Software Tools Hackers Use?
Underground software tools are advanced cybersecurity programs commonly used by ethical hackers, penetration testers, and security researchers to find vulnerabilities in systems. Tools like Burp Suite and Nmap help professionals test networks and applications legally to improve security rather than exploit weaknesses.
Are these hacking tools legal to use?
Yes, these tools are completely legal when used with permission. Software such as Metasploit Framework and Wireshark is widely used by cybersecurity experts, companies, and educational institutions for ethical hacking, vulnerability testing, and system auditing.
Who uses underground hacking tools?
Ethical hackers, cybersecurity analysts, penetration testers, IT administrators, and digital forensic investigators regularly use these tools. Platforms like Maltego help researchers gather open-source intelligence, while organizations use security tools to prevent cyberattacks and data breaches.
Can beginners learn these tools safely?
Yes. Beginners can start learning cybersecurity using controlled labs and legal environments. Tools such as Nikto and SQLmap are commonly taught in ethical hacking courses to help learners understand vulnerabilities responsibly.
Why do ethical hackers use password-testing tools?
Password auditing tools like John the Ripper and Hydra are used to identify weak authentication systems. Companies use them legally to enforce stronger passwords and implement multi-factor authentication for better protection.