I will be writing about the Best Digital Authentication and Online Privacy Options: (Best Decentralized Identity (DID) Auth Providers.) Identity, Decentralized identity solutions allow users to take back control of the data format, authenticate passwords and provide better cybersecurity in Web3s to enterprise solution.
In this article, we will discuss about the leading DID Platforms and its features & benefits and how they are paving towards a secure digital identity management.
Key Point & Best Decentralized Identity (DID) Auth Providers
| Provider | Key Points |
|---|---|
| Microsoft Entra Verified ID | Enterprise-grade decentralized identity solution enabling verifiable credentials, passwordless authentication, strong compliance, and seamless integration with Microsoft cloud ecosystem. |
| IBM Digital Credentials | Blockchain-based credential verification platform focused on trusted digital certificates, workforce identity validation, and secure enterprise credential management. |
| Sovrin Network | Public-permissioned decentralized identity network built on self-sovereign identity principles with global trust framework and privacy-first credential exchange. |
| Evernym (Avast/Gen) | Pioneer of self-sovereign identity solutions offering decentralized wallets, credential issuance tools, and privacy-preserving authentication infrastructure. |
| Bloom Protocol | Decentralized identity and credit scoring protocol allowing users to own identity data while enabling trusted reputation and financial verification. |
| Civic Identity | Consumer-focused identity verification platform providing reusable KYC credentials, secure login authentication, and fraud prevention using blockchain technology. |
| KILT Protocol | Open-source blockchain protocol enabling anonymous credentials, decentralized identifiers, and selective data disclosure for Web3 applications. |
| SelfKey | Self-sovereign identity ecosystem with digital identity wallet allowing users to control personal data and access crypto and financial services securely. |
| ShoCard | Blockchain identity authentication system using cryptographic verification to protect user identity and simplify secure access management. |
| Veramo (Open Source) | Developer-focused open-source framework supporting DID management, verifiable credential creation, and integration into decentralized applications. |
1. Microsoft Entra Verified ID
Microsoft Entra Verified ID is a decentralized identity solution based on W3C Decentralized Identifier (DID) and Verifiable Credential standards. Is able to activate the issuing, verification and management of digital credentials without having sensitive personal data stored in a central register. Identity information is owned by individuals and placed in secure wallets, this allows for passwordless authentication and privacy-first access management.
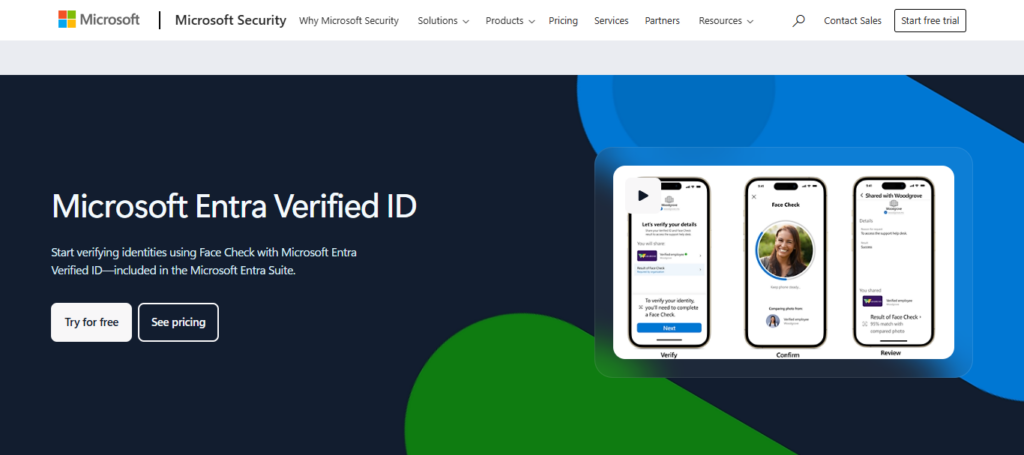
It is used by enterprises for onboarding new employees, education credentials and secure login validation. Microsoft Integrated Partner as one of the Best Decentralized Identity (DID) Auth Providers, Well integrated with Microsoft Entra and Azure ecosystems— better at zero-trust security models, compliance, interoperability, and scalability benefits for modern digital services.
Microsoft Entra Verified ID – Feature
- Follow W3C decentralized identity standards and verifiable credentials.
- Facilitates authentication without a password and serves as an identity passport.
- Goes hand-in-hand with Microsoft products, Azure and enterprise apps
- Selective disclosure: Users can control the identity data that is shared.
- Trust Frameworks backed by Blockchain to Validate Credentials
Microsoft Entra Verified ID — Pros & Cons
| Pros | Cons |
|---|---|
| Strong enterprise-grade security backed by Microsoft ecosystem | Requires Microsoft cloud environment |
| Supports W3C decentralized identity standards | Setup can be complex for beginners |
| Seamless integration with Azure & Microsoft 365 | Licensing costs for advanced features |
| Passwordless authentication support | Less flexible outside Microsoft stack |
| Trusted enterprise adoption worldwide | Dependency on Microsoft infrastructure |
2. IBM Digital Credentials
IBM Digital Credentials — Verification on the Blockchain with Decentralized Identifiers and Verifiable Credentials. It allows institutes, universities and enterprises to issue practically impossible-to-fake digital certificates & professional credentials.
Support cross-industry credential verification while keeping identity data owned by users with a multi-ledger compatible design and open standards architecture Faster trust validation workflows reduce fraud for organizations.
IBM : An innovator placed on our list of Best Decentralized Identity (DID) Auth Providersprovides enterprise trust frameworks, compliance automation and interoperability by allowing for secure sharing of identity information without needing a centralized identity7096 repository or the need to have traditional password login system.
IBM Digital Credentials – Features
- Provides a trader to declare a solution of issues forged digital certificates or verifiable credentials.
- Verification of identity through Blockchain technology ensuring trust and transparency
- Verifies achievement with academic, workforce and enterprise credentials.
- Supports automatic issuance and management of credentials throughout their lifecycle.
- Compatible with worldwide decentralized identity ecosystems
IBM Digital Credentials — Pros & Cons
| Pros | Cons |
|---|---|
| Enterprise blockchain credential verification | Higher implementation cost |
| Strong compliance & governance features | Requires technical expertise |
| Supports verifiable credentials standards | Not ideal for small startups |
| Scalable identity infrastructure | Complex deployment process |
| Trusted brand for enterprise identity | Limited consumer-focused tools |
3. Sovrin Network
The self-sovereign identity (SSI) Sovrin Network is a global public utility Using distributed ledger tech, it allows users and groups to formulate decentralized identifiers without the use of central entities. Sovrin’s decentralized governance proofs, carried out through a small number of trusted stewards acting as a stabilizing force for the global network while remaining true to decentralization.
Through digital identity wallets, users handle credentials and disclose personal data selectively. Sovrin being one of the Best Decentralized Identity (DID) Auth Providers does focus on Privacy, Trust Registries & Global Interoperability whilst helping governments, healthcare providers and enterprises deploy scalable identity verification solutions that keep users in control and secure using cryptographic authentication.
Sovrin Network – Features
- A public permissioned blockchain for SSI
- Layer for global governance of decentralized identifier (DID) infrastructure.
- Privacy-preserving authentication without centralized authorities.
- Provides verifiable credentials between companies and government systems.
- An ecosystem of open-source maintained by decentralized stewards.
Sovrin Network — Pros & Cons
| Pros | Cons |
|---|---|
| Fully decentralized public identity network | Governance model may feel complex |
| Open standards and interoperability | Requires understanding of SSI concepts |
| Privacy-first architecture | Limited enterprise UI tools |
| No central authority control | Adoption still growing |
| Community-driven ecosystem | Integration effort required |
4. Evernym (Avast/Gen)
Evernym, a member of Gen Digital within Avast, is an early leader in decentralized identity and self-sovereign identity technology. It fostered lots of the basic building blocks SSI concepts and tools that enable decentralized identifiers (DIDs) and verifiable credential exchange.
The company provides the technology to help build secure digital identity wallets, credential issuing and verification platforms and trust networks for both government and enterprise. From Sovrin-based identity infrastructure it has a very decently large contribution,
A: Over the years, Evernym, now a pioneer on the list of Best Decentralized Identity (DID) Auth Providers, has stressed user-controlled authentication for returning to web-fueled personal data entry by offering private & keyed cryptographic proof that provides cross-organization identity verification without any passwords and third-party authentication authorities in between.
Evernym (Avast/Gen) – Features
- For those unfamiliar, founder of self-sovereign identity (SSI) Wallet technology.
- Offers both secure agents for identity and equivalent credential exchange capabilities.
- Based on decentralized trust frameworks such as that created by Sovrin.
- Enables enterprise-grade identity verification workflows.
- Facilitates reusable digital identity credentials between services.
Evernym (Avast/Gen) — Pros & Cons
| Pros | Cons |
|---|---|
| Pioneer of Self-Sovereign Identity (SSI) | Enterprise setup complexity |
| Built on decentralized trust frameworks | Commercial support availability varies |
| Strong credential issuance tools | Smaller ecosystem compared to Microsoft |
| High privacy protection | Requires SSI knowledge |
| Compatible with Sovrin network | Learning curve for organizations |
5. Bloom Protocol
Bloom Protocol is a portable identity verification and reputation system over blockchain technology for the financial and Web3 ecosystems. It allows users to build digital identitiesCredit and reputation while not sharing sensitive data with centralised database. With the use of verifiable credentials and decentralized identifiers, Bloom allows itself for trust scroing, lending verification, and fraud prevention.
Bloom Protocol focuses on people by making it easier to prove identity and credibility from anywhere in the world — charging DeFi platforms, lenders-depositors, and marketplaces with validating users seamlessly while shielding all parties at respective levels over privacy and user-data profit-ownership wine-directories Vaccine.
Bloom Protocol – Features
- Global credit and reputation scoring linked to decentralized identity.
- Identity verification and fraud prevention on the blockchain.
- Facilitates cross-border use of portable financial identity
- User Controls Identity, Privacy Primero
- Applicable for DeFi, lending and fintech identity verification.
Bloom Protocol — Pros & Cons
| Pros | Cons |
|---|---|
| Decentralized credit & reputation identity | Focused mainly on financial identity |
| Blockchain-based verification | Limited enterprise adoption |
| User-owned identity credentials | Ecosystem still evolving |
| Fraud-resistant identity scoring | Integration options limited |
| Useful for DeFi applications | Regulatory uncertainty in some regions |
6. Civic Identity
Civic is an open-source identity verification ecosystem built on the blockchain that enables access to secure digital wallets and reuse of credentials. Users verify their identify one time, and reuse verified credentials to authenticate with different providers without using personal information each time.
Civic aims to provide fraud prevention, compliance verification and passwordless authentication for applications in Web3, fintech and enterprise. Civic empowers businesses to optimize onboarding friction while enhancing privacy protection, making it a strong candidate for why its listed as one of the **Best Decentralized Identity (DID) Auth Providers.
With its decentralized design, it protects personal identity information in users’ hands while providing trusted verification results to organizations through security techniques like cryptographic authentication methods as evidence.
Civic Identity – Features
- An identity-based wallet for mobile-first experiences.
- Verified identity credentials for passwordless login
- Blockchain verification and biometric authentication.
- Lowers KYC costs for businesses and fintech platforms.
- Identity consumable with lesser information exposure by user controlling
Civic Identity — Pros & Cons
| Pros | Cons |
|---|---|
| Mobile-first decentralized identity wallet | Dependent on mobile usage |
| Fast identity verification | Limited enterprise customization |
| Reduces KYC onboarding friction | Smaller developer ecosystem |
| Blockchain-backed authentication | Requires user education |
| Good for fintech onboarding | Less suited for complex enterprises |
7. KILT Protocol
KILT Protocol is open blockchain identity infrastructure for issuing decentralized credentials & digital attestations. It is developed based on the Polkadot ecosystem and allows developers to design identity authentication solutions without centralized entities. For example, KILT allows for selective disclosure so that users share only the necessary identity attributes rather than their full personal profile.
Voted in Top Decentralized Identity (DID) Auth Providers, KILT Protocol allows enterprise, government and Web3 applications to create trusted unique digital identities with zero-knowledge, compliance and interoperability. The decentralised governance of offers transparent credential validation and secure authentication for decentralized applications and digital services.
KILT Protocol – Features
- The Decentralized Identity built on Substrate blockchain
- Decentralized identity without on-chain data storage.
- Provides anonymous authentication and selective disclosure.
- Provides trust market base for verifying credentials.
- A real emphasis on both Web3 privacy and decentralized governance.
KILT Protocol — Pros & Cons
| Pros | Cons |
|---|---|
| Built on Polkadot ecosystem | Requires Web3 familiarity |
| Privacy-preserving credentials | Smaller adoption compared to big vendors |
| Supports selective disclosure | Development complexity |
| Open-source infrastructure | Limited enterprise tools |
| Strong Web3 interoperability | Still expanding ecosystem |
8. SelfKey
SelfKey are a self-sovereign identity platform that give people & organizations back complete ownership of their digital identity data. Identity documents are stored in the users own encrypted wallet that only they have access to, and verified credentials can be shared as needed. SelfKey combines identity verification with financial services, company formation apps, and compliance onboarding tools.
In Best Decentralized Identity (DID) Auth Providers, SelfKey’s privacy-by-design architecture avoids risks associated with centralized storage of identity. Through the principles of identity ownership, SelfKey is able to put this functionality into action by letting users to retain full potential control over their own digital identity—without losing the certainty of verification through blockchain regulatory compliance and providing a way for users to safely authenticate themselves on cross-border – at cost effective solution for safety against data breaches and unauthorized access.
SelfKey – Features
- Crypto and KYC integrations with self-sovereign identity wallet
- Enables secure management of digital identity documents by users.
- Allows for immediate onboarding to financial services.
- Blockchain-based identity ownership and control.
- Marketplace integration for identity-based services.
SelfKey — Pros & Cons
| Pros | Cons |
|---|---|
| Self-sovereign identity ownership | UI not as modern as competitors |
| Crypto & identity wallet integration | Focused heavily on crypto users |
| Reduces centralized data storage risks | Limited enterprise features |
| User-controlled KYC credentials | Smaller developer community |
| Marketplace-based identity services | Adoption niche-specific |
9. ShoCard
Founded in 2015, ShoCard provides blockchain based digital identity verification for enterprises and mobile identity recognition. It enables people to keep authentic credentials on a personal device but record identity proofs in a distributed ledger for verification. ShoCard works with banking, travel, healthcare and workforce access systems for personalized mining.
As One of the Best Decentralized Identity (DID) Auth Providers, ShoCard eliminates identity-related fraud by eliminating the password and using a combination of cryptographic verification & digitally-signed credentials to verify a user.
Ivory enables enterprises to move with a forward-thinking mindset, as they can onboard users securely and in accordance to regulations but also allows for decentralized verification of credentials which secures ownership of the user, while allowing enterprises to achieve trustless authentication without maintaining centralized databases.
ShoCard – Features
- Secure identity verification using blockchain anchoring
- IDWallet for Mobile authentication and access control.
- Eliminates centralized identity databases.
- Includes enterprise login and credential verification
- Immutable identity records through strong encryption
ShoCard — Pros & Cons
| Pros | Cons |
|---|---|
| Blockchain-secured identity verification | Less active ecosystem growth |
| Easy digital ID management | Limited public documentation |
| Secure credential sharing | Enterprise adoption moderate |
| Strong encryption model | Smaller community support |
| Useful for authentication workflows | Fewer integrations available |
10. Veramo (Open Source)
Veramo is an open-source decentralized identity framework that developers are building DID and verifiable credential applications. Compatible with a wide range of blockchain networks, it offers the following modular tools/APIs/SDKs for managing decentralized identifiers, credential issuance and authentication workflows:
With Veramo’s support for interoperability standards, developers can seamlessly integrate decentralized identity into their Web3 apps, wallets and enterprise platforms.
Veramo, one of the Best Decentralized Identity (DID) Auth Providers. Veramo can help innovators due to its open architecture and facilitating flexible agent frameworks with customizable identity agents that scale, yields a vendor lock in free self-sovereign identity systems for organizations and developers.
Veramo (Open Source) – Features
- Django-LDAPOpen-source app framework for DID and verifiable credential apps
- Quick way to build quickly developer friendly SDK ms store multi-did method.
- Tilting the architecture of identity agents and wallets
- Compatible with Ethereum and all the blockchain ecosystems.
- Perfect for composable decentralized identity authentication systems.
Veramo (Open Source) — Pros & Cons
| Pros | Cons |
|---|---|
| Fully open-source DID framework | Requires developer expertise |
| Highly customizable identity stack | No out-of-box enterprise UI |
| Supports multiple DID methods | Setup time can be longer |
| Ideal for Web3 builders | Requires hosting & maintenance |
| Flexible plugin architecture | Not beginner-friendly |
Conclusion
In short, decentralized identity brings the control of digital personal data from a centralized environment to individual users, and will change digital security forever. Microsoft Entra Verified ID, IBM Digital Credentials,
Sovrin Network and Evernym are all heavy hitters in the enterprise identity trust space, while newcomers such as Bloom Protocol, Civic Identity and KILT Protocol pioneer approximately at the behest of Web3 adoption for true self sovereign identity practices with privacy by default credentialing.
On the other hand, self-sovereign ecosystems like SelfKey and ShoCard and developer frameworks such as Veramo further increase the reach for people and builders. As a group, these Best-DID Auth Providers Login Facilitators provide passwordless login, fraud reduction, regulatory compliance and security for digital interaction.
Decentralized Identity solutions are at the core of our next generation internet — where trust is provably settled, authorization through cryptographic consent, and identity belongs to YOU.
FAQ
What are Decentralized Identity (DID) authentication providers?
Decentralized Identity (DID) authentication providers are platforms that allow users to control and manage their digital identity without relying on centralized databases. Solutions like Microsoft Entra Verified ID and Sovrin Network use blockchain or distributed technologies to verify credentials securely while protecting personal data privacy.
How do DID authentication systems work?
DID systems use decentralized identifiers and verifiable credentials stored in digital wallets. Platforms such as IBM Digital Credentials issue cryptographically signed credentials that users can share selectively, enabling secure authentication without passwords or centralized storage.
Why are decentralized identity providers important?
They reduce data breaches, eliminate password dependency, and give users ownership of personal information. Providers like Civic Identity and Bloom Protocol help organizations verify identities while minimizing privacy risks and regulatory challenges.
Are DID authentication providers secure?
Yes. Most Best Decentralized Identity (DID) Auth Providers use encryption, blockchain verification, and zero-trust security models. Solutions such as KILT Protocol and ShoCard rely on cryptographic proof instead of passwords, significantly reducing fraud and identity theft risks.