Today, I want to cover the Best Zero-Trust Architecture Software for remote teams. It also introduces top security platforms that enable organizations to better secure their remote working environment.
With the rise of Cyber Crime, Zero-Trust solutions provide an answer for secure access and identity verification with continuous monitoring. In this guide, we explore the leading ZTA tools to help your company become stronger by securing, enhancing productivity and protecting distributed teams with IAM.
What is Zero-Trust Architecture (ZTA)?
Zero-Trust Architecture (ZTA) is a cyber security framework of the new age based on the philosophy of trust never, verify ever. Traditionally, networks take the approach of trusting users or machines that reside inside an environment — but ZTA is different; it continually authenticates identities, validates device security and assesses access requests before allowing requesting applications or data.
It eliminates conventional network boundaries with least-privilige access and constant monitoring. Such an approach enables organizations to secure sensitive information, safeguard against unauthorized access and protect cloud environments, remote employees or hybrid infrastructures from ever-evolving cyber threats.
Why Zero-Trust Architecture Software for Remote Teams
Secure Remote Access Anywhere
Remote employees make use of multiple locations and networks. In a nutshell, Zero-Trust software checks each and every login request so that only those who are supposed to be accessing company resources do so.
Protection Against Cyber Threats
With ZTA, administrators can monitor the behaviour of users and security of devices to safeguard against phishing, ransomware and credential based attacks targeting remote workers.
Eliminates Traditional VPN Risks
Zero-Trust provides application-level access, which exposes fewer internal systems rather than granting access to the entire network like VPNs do.
Identity-Based Security Controls
Network location is irrelevant when it comes to access decisions proactive and based on what? Identity contextual information — device health, 3rd party verification, geographical location risk level.
Cloud & Hybrid Work Environment Ready
Zero-Trust also integrates with billions of cloud apps, SaaS platforms and modern remote team hybrid infrastructures.
Continuous Monitoring & Verification
Enabling verification of not just during login but throughout sessions, increasing an organization’s overall security posture.
Improved Compliance & Data Protection
Ensures organizations stay compliant through able access policies and audit trails
Is Zero-Trust suitable for small businesses and startups?
Absolutely, Zero-Trust Architecture is a perfect fit for small businesses and startups as it offers robust security without demanding costly or elaborate infrastructure. Cloud-native modern Zero-Trust solutions are modular, and simple to deploy making it easier for smaller organizations to shield remote employees, customer data and business applications from cyber threats.
Founders no longer need to sink money into boxy network security hardware; instead, identity-based access control, multi-factor authentication and continuous monitoring can all be enabled at accessible price points.
It allows increasing companies to keep enterprise-grade security, while enabling mobility with remote access and expediting digitally transforming operations.
Key point & Best Zero-Trust Architecture Software for Remote Teams
| Software | Key Security Features |
|---|---|
| Okta Identity Cloud | SSO, MFA, adaptive authentication, lifecycle management |
| Cisco Duo Zero‑Trust | Multi-Factor Authentication, device trust, risk-based access |
| Palo Alto Prisma Access | Secure Access Service Edge (SASE), firewall-as-a-service, threat prevention |
| Zscaler Zero Trust Exchange | Zero-trust network access, web filtering, data protection |
| CrowdStrike Falcon Zero‑Trust | AI threat detection, device posture checks, continuous verification |
| Fortinet FortiTrust | Identity verification, secure networking, threat intelligence |
| Check Point Harmony Connect | Secure web gateway, Zero-Trust Network Access (ZTNA), malware prevention |
| VMware Workspace ONE + Carbon Black | Unified endpoint management, behavioral threat detection |
| Ping Identity Zero‑Trust Suite | AI-based authentication, access governance, identity analytics |
1. Okta Identity Cloud
Okta Identity Cloud is an industry-leading identity-centric Zero-Trust platform, securing all users, applications and devices from anywhere. It focuses on SSO (single sign-on), adaptive multi-factor (MFA) authentication, and lifecycle identity management.
It constantly authenticates users identity and contextual risk for access of resources. Traditional VPN dependency can be avoided with solutions such as Best Zero-Trust Architecture Software for Remote Teams by using Okta, which enables secure login to cloud resources from anywhere on the Internet.
Okta connects 1000s of enterprise applications across hybrid environments and enforces least-privilege access to these while still providing users a seamless user experience across your remote work infrastructure.
Okta Identity Cloud Features
- Single Sign-On (SSO) —Allows employees to log into various cloud and enterprise apps securely through a single login.
- Adaptive Multi-Factor Authentication (MFA) — Conditional authentication based on device, location, and behavior.
- Universal Directory – An Identity store for Users, Devices and Applications
- Automation of Lifecycle Management – Automates onboarding, role assignment and offboarding process.
- API Access Management — Provides security for APIs and integrations used in cloud-native workflows remotely.
Okta Identity Cloud
| Pros | Cons |
|---|---|
| Strong Single Sign-On (SSO) and adaptive MFA security | Premium pricing for enterprises |
| Thousands of app integrations | Initial setup can be complex |
| Excellent identity lifecycle management | Requires skilled admin management |
| Cloud-native architecture ideal for remote teams | Dependence on internet availability |
| Powerful access automation and policy control | Advanced features increase cost |
2. Cisco Duo Zero‑Trust
Before enterprise systems are granted access, Cisco Duo Zero-Trust validates identity and attests to device trust. Its security model continuously assesses users, devices and sign-in patterns to block unauthorized access attempts. Designed for hybrid and remote workplaces, Duo has supplemented legacy perimeter security with cloud-authentication features and adaptive access policies.
Organizations consider it as one of the Best Zero-Trust Architecture Software for Remote Teams as it provides efficient access without heavy infrastructure that modern-day cyber security environments require developmentHouse Duo provides secure, dynamically adaptable policy enforcement that is integrated with VPNs, cloud apps, and on-premises systems as well as phishing resistant MFA and endpoint visibility.
Cisco Duo Zero-Trust Features
- Secure Multi-Factor Authentication — Logins secured with push notifications, biometrics and hardware tokens.
- Device Trust Verification – checks the health of a device before granting system access.
- Zero-Trust Network Access (ZTNA) – Enables secure connectivity without reliance on traditional VPN.
- Adaptive Access Policies: – Adjusts the security levels based on a users risk level.
- Deploy, and forget User Deployment – Deploy on the cloud in minutes for distributed teams of remote workers.
Cisco Duo Zero-Trust
| Pros | Cons |
|---|---|
| Easy deployment and user-friendly interface | Limited deep endpoint protection |
| Strong MFA and device verification | Advanced analytics require upgrades |
| Works across VPN and cloud apps | Less comprehensive than full SASE tools |
| Good integration with enterprise systems | Custom policies may need tuning |
| Excellent remote workforce authentication | Pricing scales with users |
3. Palo Alto Prisma Access
Palo Alto Prisma Access provides cloud native SASE capabilities with Zero-Trust alignment. By allowing for consistency in security policies both on the user, branch office and application level its able to protect users, branch offices and applications across networks & clouds.
This single architecture includes firewall-as-a-service, secure web gateway and data protection Prisma Access is considered one of the Best Zero-Trust Architecture Software for Remote Teams by enterprises as it enables secure access to applications without opening internal networks.
The process of continual traffic inspection, combined with AI-native threat prevention and fine-grained segmentation, guarantees remote employees safe connections to corporate resources while simultaneously providing performance and scale for globally distributed teams.
Palo Alto Prisma Access Features
- Cloud-Delivered Security Platform — The Secure Access to Apps and Data from Anywhere.
- Secure Web Gateway – shields users from bad websites and phishing attacks.
- ZTNA 2.0 Access Control – Authentication of identity, app or device is a continuous activity.
- Using advanced threat prevention — AI detection to automatically block ransomeware and other sophisticated attacks.
Palo Alto Networks Prisma Access
| Pros | Cons |
|---|---|
| Full SASE platform with Zero-Trust security | Higher implementation cost |
| Advanced threat prevention and AI analytics | Requires network expertise |
| Global cloud infrastructure for remote access | Complex initial configuration |
| Strong cloud and SaaS visibility | Overkill for small businesses |
| Consistent policy enforcement everywhere | Licensing structure can be confusing |
4. Zscaler Zero Trust Exchange
The Zscaler Zero Trust Exchange is a cloud security platform that connects users directly to applications rather than networks, eliminating lateral movement in the attack surface.
It authenticates identity, assesses device posture, and policy holds for every session request. With a globally distributed cloud infrastructure, it processes billions of security transactions on a daily basis to enforce least-privilege access.
Reporting has been ubiquitously acclaimed it as Best Zero-Trust Architecture software for Remote Teams since employees can receive authorization from any place on any gadget without the congestion of a VPN. It Combines Secure Internet Access, Secure Applications Access and Data Protection in a Single Scalable Zero-Trust Framework.
Zscaler Zero Trust Exchange Features
- Direct-to-Cloud connectivity — connects applications directly to users instead of providing access via a network.
- Identity-Based Access Control – Allows access to verified applications only
- Secure Internet Access(SIA) — Provides protection for browsing, SaaS access and cloud usage.
- Data loss prevention, DLP – Stops sensitive data leaking from any remote endpoint
Zscaler Zero Trust Exchange
| Pros | Cons |
|---|---|
| Eliminates traditional VPN dependency | Learning curve for administrators |
| Secure direct-to-cloud connectivity | Migration from legacy systems needed |
| Excellent performance for remote users | Enterprise pricing |
| Real-time traffic inspection | Requires architecture redesign |
| Highly scalable cloud platform | Limited on-prem flexibility |
5. CrowdStrike Falcon Zero‑Trust
CrowdStrike Falcon Zero-Trust extends endpoint security into identity-based access-control by combining EDR with Zero-Trust (ZT) assessment. Before granting resource access, it assesses device risk scores, threat intelligence and user behavior.
This minimises the attack surfaces presented by compromised endpoints or stolen credentials. Falcon is frequently listed by security leaders as one of the Best Zero-Trust Architecture Software for Remote Teams bridging endpoint protection and access management.
With zero-trust access, these continuous layers of defence mean that in an environment where suspicious activity is detected and identified, access privileges automatically adjust to mitigate threats before they can propagate throughout remote environments and cloud-first infrastructures.
CrowdStrike Falcon Zero-Trust Features
- Endpoint Detection & Response (EDR) *– Monitoring of remote devices in real-time.
- AI Threat Intelligence detects suspicious activity using behavioral analytics.
- Device Risk Scoring: This is used to determine trust level before a device is allowed access to the system.
- This Whitelist integrates with the Identity Protection service, helping mitigate stolen credential and lateral movement attacks.
- Cloud-Native Security Platform — Lightweight Deployment with Centralized Visibility
CrowdStrike Falcon Zero-Trust
| Pros | Cons |
|---|---|
| Industry-leading endpoint protection | Primarily endpoint-focused |
| AI-powered threat detection | Additional modules increase cost |
| Lightweight agent performance | Requires integration for full ZTA |
| Real-time behavioral monitoring | May need third-party identity tools |
| Strong ransomware defense | Advanced tuning recommended |
6. Fortinet FortiTrust
Fortinet FortiTrust combines networking and security services to deploy Zero-Trust Network Access (ZTNA) via FortiTrust. It brings together the unified security fabric of firewall protection, endpoint control, secure access, and identity verification.
It has enabled micro-segmentation and continuous authentication that ensures users get only access to the applications they are entitled. Because it integrates so well with existing Fortinet ecosystems, many enterprises such as Buy Best zero-trust architecture software for remote teams (FortiTrust) while also providing simplification of centralized security management.
For organizations migrating from legacy VPN architectures to a modern Zero-Trust networking approach, its AI threat intelligence that provides visibility into remote devices can fit the bill.
Fortinet FortiTrust Features
- Coming from network, endpoint and cloud security controls unified tightened.
- — Zero-Trust Network Access — Provide Secure Remote Access and at the same time keeping internal networks safe.
- *Integration with Secure SD-WAN — Optimizes performance for global remote employees.
- Always-On Monitoring – Continuous visibility of users and machines.
- Automated Detection of Cyber Threats & Response from AI-Driven Threat Intelligence
Fortinet FortiTrust
| Pros | Cons |
|---|---|
| Unified security fabric integration | Interface complexity for beginners |
| Strong network and firewall protection | Best with Fortinet ecosystem |
| Secure SD-WAN and remote access | Hardware dependency in some cases |
| Centralized security management | Licensing tiers can be complex |
| Good performance optimization | Smaller ecosystem vs competitors |
7. Check Point Harmony Connect
Check Point Harmony Connect – is a cloud-delivered security platform that serves to provide secure internet access and Zero-Trust connectivity for remote users. It aims for the best protection against phishing, ransomware and web-based attacks while continuing to authenticate identity as well. This solution sends traffic through secure cloud gateways, enabling employees to work safely from anywhere.
The robust prevention and easy deployment capabilities of Harmony Connect classify it among Best Zero-Trust Architecture Software for Remote Teams according to businesses. Integrated threat intelligence, isolated browsing from both the device and network protection and application-level access controls are capabilities that provide organizations with the ability to enable productivity without losing the security battle.
Check Point Harmony Connect Features
- Secure Access Service Edge (SASE) – A network and security service in a single platform.
- Private Applications Access – Users use applications securely without exposing VPN.
- Preventing Advanced Threats – Prevents getting drawn into phishing, malware and zero-day threats.
- Cloud Web Security – Offers security for SaaS and internet traffic of remote workers.
- Unified Management Console – Simplified policy management across distributed teams
Check Point Software Technologies Harmony Connect
| Pros | Cons |
|---|---|
| Browser-based Zero-Trust access | Limited advanced customization |
| Fast deployment for remote teams | Smaller marketplace integrations |
| Strong phishing and web protection | Reporting tools less flexible |
| Secure internet access without VPN | May require training |
| Cloud-delivered threat prevention | Enterprise features cost extra |
8. VMware Workspace ONE + Carbon Black
Integrating Endpoint management with Advanced Threat protection, VMware Workspace ONE + Carbon Black strengthen Zero-Trust environment. While Workspace ONE does identity, device management and secure application delivery, Carbon Black provides behavioral analytics and endpoint detection.
They work together to impose contextual access decisions based on user identity, device compliance and risk posture. Being able to secure laptops, mobiles and virtual desktops from a single pane of glass often leads this integrated ecosystem to be considered as best zero-trust architecture software for remote teams. Ongoing monitoring so that compromised endpoints are always revoked of priv access.
Workspace ONE + Carbon Black Features
- Unified Endpoint Management (UEM) — Allows centrally managing laptops, mobiles and any remote devices.
- Conditional Access Policies – For the access to be granted only on trusted and compliant devices.
- Machine learning– Carbon Black constantly monitors behavior on endpoints and keeps fine-tuning its algorithms to identify the things it should not be seeing happening at endpoint or network level.
- **Digital Workplace Security — Application delivery without boundaries for hybrid teams.
- Automation of Endpoint Compliance – Automatic pointless defense.
VMware Workspace ONE + Carbon Black
| Pros | Cons |
|---|---|
| Unified endpoint and identity management | Complex enterprise deployment |
| Strong device compliance enforcement | Higher licensing costs |
| Excellent remote device management | Requires VMware ecosystem familiarity |
| Advanced behavioral threat detection | Resource intensive setup |
| Supports Zero-Trust device posture | Best suited for large enterprises |
9. IBM Security Verify
IBM Security Verify: Delivers identity governance, access management and adaptive authentication based on Zero-Trust security principles. It powers AI-based risk analysis and passwordless identification along with automating identity lifecycle for an enterprise that is present on Hybrid.
This means the platform constantly authenticates users instead of a one-off authentication event. It is repeatedly utilized by organizations as Best-Zero-Trust-Architecture Software For Remote Teams, due to its simultaneous integration with cloud platforms, legacy systems and contemporary applications of SaaS.
IBM’s analytics engine analyzes behavioral signals to identify anomalous activity while providing a secure and compliant collaboration framework across distributed workforce infrastructures.
IBM Security Verify Features
- Zero-Trust Security with an Identity-centric Approach — Verifies users first, followed by access to resources.
- Adaptive Access Controls – Risk signal based context-aware authentication
- Cloud Identity Governance: – Compliance usage and permission: Audit on user – Make sure with the help of this, we will make compliance.
- Passwordless Authentication– Allows biometric and newer standards of authentication
- Hybrid Cloud Integration — Connects legacy systems and cloud applications.
IBM Security Verify
| Pros | Cons |
|---|---|
| Enterprise-grade identity governance | Implementation takes time |
| Strong AI risk-based authentication | Interface less modern |
| Hybrid cloud and legacy support | Requires skilled administrators |
| Regulatory compliance capabilities | Higher enterprise pricing |
| Scalable authentication platform | Smaller app ecosystem |
10. Ping Identity Zero‑Trust Suite
Ping Identity Zero-Trust Suite provides intelligent identity orchestration and secure digital experiences. It unifies Single Sign-On, identity federation, adaptive authentication and API security in one platform.
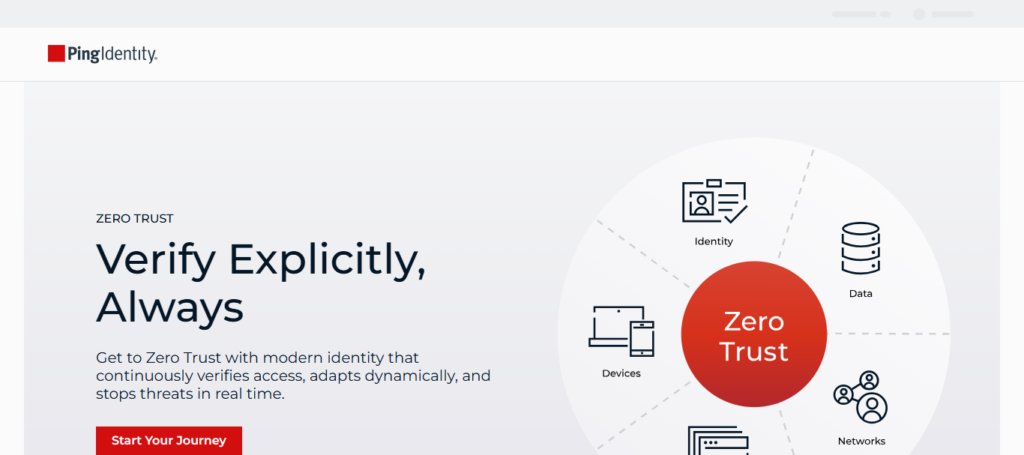
The solution allows organizations to define fine-grained access policies that factor different contextual risk signals — such as the location, device hygiene status and behavioral patterns of the user. Ping Identity is listed as one of the Top Zero-Trust Architecture Software for Remote Teams by a number of cybersecurity subject matter experts due to its penetration into multi-cloud and hybrid infrastructure.
The strong identity federation capabilities enable enterprises to securely connect employees, partners and customers without exposing internal networks.
Ping Identity Zero-Trust Suite Features
- Federated Identity Management – Authenticate securely across multiple platforms and services.
- Single Sign-On & MFA – A seamless and secure experience for all your remote teams.
- API Security Protection – This protects the APIs that are used by remote applications.
- Intelligent Access Policies * – AI Based Risk Assessment Prior to Approving Access
Ping Identity Zero-Trust Suite
| Pros | Cons |
|---|---|
| Flexible identity federation | Setup complexity for beginners |
| Strong API and workforce identity tools | Requires technical expertise |
| Adaptive authentication policies | Premium enterprise pricing |
| Works across hybrid environments | Limited SMB focus |
| Excellent customer identity management | Integration planning required |
Conclusion
Best Zero-Trust Architecture Software for Remote Teams Because of how prevalent cloud-first and hybrid work models have become, this is an area that every organisation will want to make the right choice with.
By continuously confirming that users, devices and access requests are valid before granting permissions, Zero-Trust security does away with the traditional notion of network boundaries altogether. Identity-based platforms, cloud-delivered security services, and endpoint-driven protection all play an important role in reducing cyber risk while enabling businesses to operate with as little friction as possible.
Choosing the right zta software is highly dependent on company size, infrastructure complexity, universal mobile workforce distribution and compliance requirements. Using this Zero-Trust approach to data security means organizations can quarantine, protect and keep unauthorized access away from data while providing secure and confident support for remote employees anywhere across the world.
FAQ
What is Zero-Trust Architecture (ZTA)?
Zero-Trust Architecture is a cybersecurity model based on the principle of “never trust, always verify.” Instead of trusting users inside a network, ZTA continuously verifies identity, device health, and access permissions before allowing access to applications or data.
Why do remote teams need Zero-Trust security?
Remote employees access company systems from different locations and devices, increasing cyber risks. The Best Zero-Trust Architecture Software for Remote Teams protects organizations by enforcing identity verification, device checks, and secure access controls without relying on traditional VPN security.
How does Zero-Trust differ from traditional VPN security?
Traditional VPNs grant broad network access after login, while Zero-Trust provides application-level access only. ZTA continuously validates users and devices throughout sessions, minimizing lateral movement and preventing unauthorized access.
Is Zero-Trust suitable for small businesses and startups?
Yes. Modern cloud-based ZTA platforms offer scalable pricing and easy deployment, making Zero-Trust security accessible to startups, SMEs, and enterprises alike without heavy infrastructure investments.